The North Korean state-linked threat group Kimsuky has expanded its attack methods by distributing a dangerous…
Continue ReadingTag: code
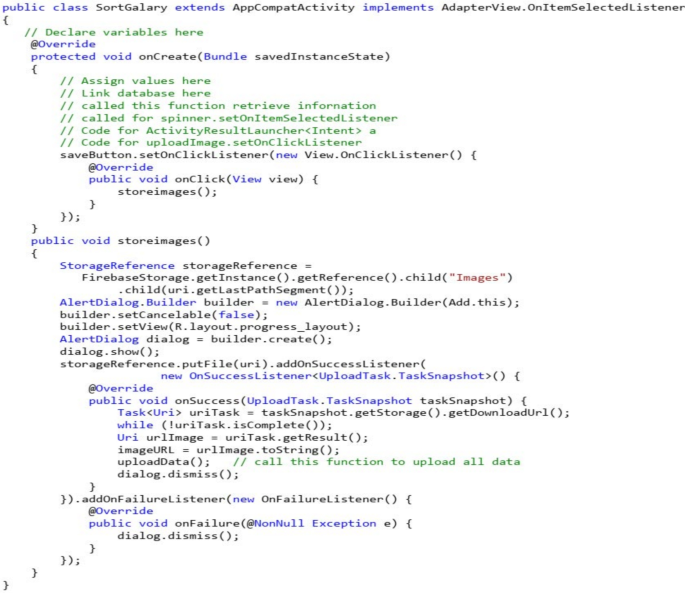
Deep multi-metrics learning for mobile app defect prediction using code and process metrics
The design of the experiments conducted in this study, along with the subsequent analysis and discussion…
Continue Reading
From Code to Context: How Spatial AI is Powering the Next Leap in Manufacturing
Beyond the data-driven efficiencies of Industry 4.0, a new paradigm is emerging for manufacturers across every…
Continue Reading
How a chain of security flaws exposed thousands of enterprise surveillance cameras to remote code execution
Image created with ChatGPT Security researchers have uncovered a chain of four vulnerabilities in popular Axis…
Continue Reading
